Best Free Folder Lock Softwares

The Best Encryption Software of 2. Encrypt Everything! Every time I hear about a scandal involving leaked documents, I wonder to myself, why weren't they encrypted? Encryption is everywhere, after all. Chrome now puts a little warning marker in the Address Bar next to any non- secure HTTP address. Google is giving HTTPS links precedence in search results over plain, unsecured HTTP links.
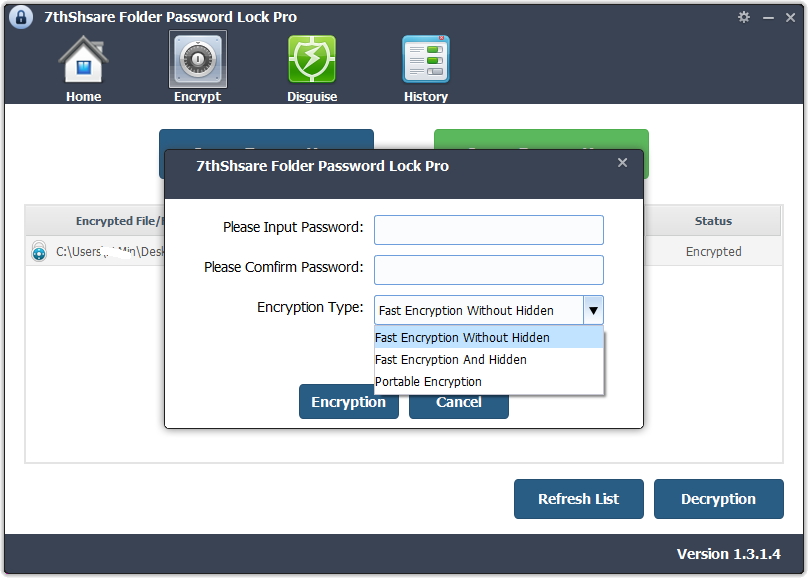
Folder Lock 7 locks, hides, and password-protects files and folders on your PC, but it also encrypts files and email attachments, takes secure backups. Free download of Folder Password Expert, security software to password protect and lock folders on a desktop, laptop, flash drive, USB external drive, thumb drive. LockHunter is a foolproof file unlocker It is a free tool to delete files blocked by something you do not know. LockHunter is useful for fighting against malware, and.
If you encrypt all of the sensitive documents on your desktop or laptop, a hacker or laptop thief won't be able to parley their possession into identity theft, bank account takeover, or worse. You can also safely share those encrypted documents with others, transmitting the decryption password under separate cover. To help you select an encryption product that's right for your computer, we've rounded up a collection of current products. As we review more products in this area, we'll update the list.
Folder Lock v7.7.0 Latest Version is a full suite solution letting you keep your files encrypted and locked while keeping an automatic and real-time backup of. Download a Windows software program to password protect folders against unwanted access.
File Encryption, Whole- Disk Encryption, and VPNs. In this roundup, I'm specifically looking at products that encrypt files, not at whole- disk solutions like Microsoft's Bitlocker. Whole- disk encryption is an effective line of defense for a single device, but it doesn't help when you need to share encrypted data. You can use a Virtual Private Network, or VPN, to encrypt your own internet traffic. From your PC to the VPN company's server, all your data is encrypted, and that's a great thing. However, unless you're connected to a secure HTTPS website, your traffic is not encrypted between the VPN server and the site. And of course the VPN's encryption doesn't just magically rub off on files you share.
Using a VPN is a great way to protect your internet traffic when you're traveling, but it's not a solution for encrypting your local files. No Back Doors. When the FBI needed information from the San Bernardino shooter's i. Phone, they asked Apple for a back door to get past the encryption. But no such back door existed, and Apple refused to create one. The FBI had to hire hackers to get into the phone. Why wouldn't Apple help? Because the moment a back door or similar hack exists, it becomes a target, a prize for the bad guys.
It will leak sooner or later. In a talk at Black Hat this past summer, Apple's Ivan Krstic revealed that the company has done something similar in their cryptographic servers.
In our 2015 review of the top free folder synchronization utility, we found some programs we could recommend with the best of these as good as any commercial product. You can easily lock a folder with this folder lock software. It is very secure. Your files will be password protected. Folder Lock is a complete data security software solution to lock files and folders with on-the-fly AES 256 bit military grade encryption. Free download.
Once the fleet of servers is up and running, they physically destroy the keys that would permit modification. Apple can't update them, but the bad guys can't get in either. All of the products in this roundup explicitly state that they have no back door, and that's as it should be.
It does mean that if you encrypt an essential document and then forget the encryption password, you've lost it for good. Two Main Approaches. Back in the day, if you wanted to keep a document secret you could use a cipher to encrypt it and then burn the original.
Or you could lock it up in a safe. The two main approaches in encryption utilities parallel these options. One type of product simply processes files and folders, turning them into impenetrable encrypted versions of themselves. The other creates a virtual disk drive that, when open, acts like any other drive on your system. When you lock the virtual drive, all of the files you put into it are completely inaccessible.
Similar to the virtual drive solution, some products store your encrypted data in the cloud. This approach requires extreme care, obviously. Encrypted data in the cloud has a much bigger attack surface than encrypted data on your own PC.
Which is better? It really depends on how you plan to use encryption. If you're not sure, take advantage of the 3. Secure Those Originals. After you copy a file into secure storage, or create an encrypted version of it, you absolutely need to wipe the unencrypted original. Family Activities Near Lancaster Pa Zip Code.
Just deleting it isn't sufficient, even if you bypass the Recycle Bin, because the data still exists on disk, and data recovery utilities can often get it back. Some encryption products avoid this problem by encrypting the file in place, literally overwriting it on disk with an encrypted version. It's more common, though, to offer secure deletion as an option. If you choose a product that lacks this feature, you should find a free secure deletion tool to use along with it. Overwriting data before deletion is sufficient to balk software- based recovery tools. Hardware- based forensic recovery works because the magnetic recording of data on a hard drive isn't actually digital. It's more of a waveform.
In simple terms, the process involves nulling out the known data and reading around the edges of what's left. If you really think someone (the feds?) might use this technique to recover your incriminating files, you can set your secure deletion tool to make more passes, overwriting the data beyond what even these techniques can recover.
Encryption Algorithms. An encryption algorithm is like a black box.
Dump a document, image, or other file into it, and you get back what seems like gibberish. Run that gibberish back through the box, with the same password, and you get back the original. The U. S. Even those that support other algorithms tend to recommend using AES. If you're an encryption expert, you may prefer another algorithm, Blowfish, perhaps, or the Soviet government's GOST. For the average user, however, AES is just fine.
Public Key Cryptography and Sharing. Passwords are important, and you have to keep them secret, right? Well, not when you use Public Key Infrastructure (PKI) cryptography.
With PKI, you get two keys. One is public; you can share it with anyone, register it in a key exchange, tattoo it on your forehead—whatever you like. The other is private, and should be closely guarded.
If I want to send you a secret document, I simply encrypt it with your public key. When you receive it, your private key decrypts it. Simple! Using this system in reverse, you can create a digital signature that proves your document came from you and hasn't been modified. Using Microsoft Project For Multiple Projects In Visual Studio. Just encrypt it with your private key. The fact that your public key decrypts it is all the proof you need. PKI support is less common than support for traditional symmetric algorithms.
If you want to share a file with someone and your encryption tool doesn't support PKI, there are other options for sharing. Many products allow creation of a self- decrypting executable file. You may also find that the recipient can use a free, decryption- only tool. What's the Best? Right now there are three Editors' Choice products in the consumer- accessible encryption field. The first is the easiest to use of the bunch, the next is the most secure, and the third is the most comprehensive. Ax. Crypt Premium has a sleek, modern look, and when it's active you'll hardly notice it.
Files in its Secured Folders get encrypted automatically when you sign out, and it's one of the few that support public key cryptography. Certain. Safe Digital Safety Deposit Box goes through a multistage security handshake that authenticates you to the site and authenticates the site to you. Your files are encrypted, split into chunks, and tokenized.
Then each chunk gets stored on a different server. A hacker who breached one server would get nothing useful. Folder Lock can either encrypt files or simply lock them so nobody can access them. It also offers encrypted lockers for secure storage.
Among its many other features are file shredding, free space shredding, secure online backup, and self- decrypting files. The other products here also have their merits, too, of course. Read the capsules below and then click through to the full reviews to decide which one you'll use to protect your files. Have an opinion on one of the apps reviewed here, or a favorite tool we didn't mention? Let us know in the comments. MSRP at Bottom Line: Ax.
Crypt Premium makes encryption simple enough for any user, and even offers public key cryptography for secure sharing of encrypted files. Read Full Review$1. MSRP at Bottom Line: When backing up your sensitive files to the cloud, Certain.
Lock and Hide Folder. After purchase you will receive your registration code and a personal link with reg code. If you have already downloaded the program and installed it running the 1. DO NOT need to reinstall the program. Simply enter the registration code at program launch.
At checkout, simply select . Paypal does not require you to open an account with them to make the credit card purchase. Paypal is a very secure terminal and your information will not be shared with any 3rd parties including UP Software.